We’re offering 20% off until Friday, March 27th. Use code NL20 when booking to apply your discount.
Big Story
How Unmanaged Machine Identities Expand API Risks
AI agents and automated workflows are introducing new categories of API consumers that existing access control models were not designed to manage.
Credential sprawl, including API tokens, SSH keys, and environment secrets distributed across endpoints and pipelines, is increasing operational complexity.
Authentication approaches centered on user sessions are insufficient when automated systems interact with APIs continuously.
Machine identity governance requires lifecycle controls comparable to those applied to human identities.
Machine-initiated API interactions are becoming a standard pattern across software delivery and platform environments. Automated consumers such as agents, orchestration tooling, background services, and deployment workflows rely on persistent credentials to access internal and external systems. These credentials are frequently generated outside centralized identity processes and distributed across developer devices, infrastructure automation layers, and runtime environments.
As the number of automated consumers increases, organizations are encountering challenges in maintaining consistent ownership, visibility, and control over machine credentials. In many environments, tokens and keys accumulate over time without clear lifecycle management or defined accountability. This creates operational risk that is often linked to permission scope, credential rotation practices, and dependency mapping.
Identity tooling is evolving to provide better insight into how credentials are created, stored, and used across distributed systems. Capabilities such as centralized secret management, endpoint-level monitoring, and automated policy enforcement are becoming part of platform governance models. This reflects a shift in focus from managing access events at runtime toward managing the conditions under which access is granted and maintained.
For API and platform teams, these changes introduce new requirements. Automated consumers must be provisioned with scoped permissions aligned to specific execution contexts, supported by revocation mechanisms and monitoring processes that match deployment velocity. Governance frameworks must also account for the dynamic nature of machine-driven interactions, where credentials may be created or modified as part of routine development and delivery workflows.
As agent-driven execution models continue to expand, machine identity management is increasingly integrated into broader API governance practices. Ensuring consistent control over credential lifecycles, usage patterns, and system dependencies becomes essential for maintaining reliable service coordination across distributed architectures.
Ultimately, this shift necessitates a unified identity-first security step that treats machine credentials as dynamic assets rather than static configurations. As the boundary between development pipelines and production environments continues to blur, the ability to correlate a specific API call back to a verified machine origin and its associated business logic will define the next generation of platform resilience.
API Feed
Know the Latest from the World of APIs
Cloudflare moved its AI Security for Apps capability to general availability, adding automated discovery of LLM-driven API endpoints and real-time detection of prompt injection and sensitive data exposure. AI-specific threat controls are now integrated into the same enforcement layer used for existing application and API security policies.
1Password introduced Unified Access, expanding identity governance to include machine credentials such as API tokens, SSH keys, and environment secrets distributed across endpoints and workflows. The platform adds device-level visibility and programmatic access controls through a new Users API, reflecting its focus on managing non-human identity lifecycles alongside traditional access management systems.
Stripe previewed tooling to meter and bill AI inference usage through its billing infrastructure, allowing software providers to track token consumption across model providers and apply configurable pricing. The development highlights alignment between API consumption patterns and financial governance models as AI workloads introduce variable operational cost structures.
Google updated Apigee’s integrated developer portal to support AsyncAPI specifications, enabling teams to publish documentation for asynchronous and event-driven interfaces alongside REST APIs. This reduces fragmentation in how streaming and event-based API surfaces are exposed to developers.
Community Spotlight
Dick Hardt: Identity, OAuth, and Agentic Trust
Dick Hardt is a foundational figure in the evolution of digital identity, best known as the author of OAuth 2.0 and JSON Web Tokens. His career focuses on the technical and philosophical frameworks of Identity 2.0, providing the essential protocols that allow applications and autonomous systems to interact securely without compromising user credentials. Hardt’s work translates complex security requirements into global standards that power the modern API economy and the emerging world of agentic AI.
Hardt’s research and development frequently examine the friction between security and user experience. Through his leadership in the OpenID Foundation and the creation of the Grant Negotiation and Authorization Protocol, he has explored how authorization must evolve to support multi-device and multi-agent ecosystems. This perspective places identity as a tool that enables verifiable trust between autonomous digital workers and enterprise data.
His contributions have been a staple of the identity and API community for decades, from his viral Identity 2.0 keynotes to technical leadership at companies like Microsoft and Amazon. Hardt has been a frequent speaker at major industry events where he provides practitioner-oriented insights into how identity standards must shift from human-to-machine toward more complex machine-to-machine interactions.
A distinctive aspect of Hardt’s recent work is his focus on the Interoperability Profiling for Secure Identity in the Enterprise working group. Through this initiative, he examines how AI agents can securely navigate fragmented SaaS environments. These studies investigate how standardized identity profiles and runtime authorization can prevent token abuse and ensure that AI agents operate within strictly governed, verifiable scopes of authority.
Across these projects, Hardt’s central argument is that the future of the internet depends on Authorization (AuthZ) rather than just Authentication (AuthN). He argues that as we move toward an agentic enterprise, the ability to prove what a system is allowed to do is vital. Well-governed identity protocols can reduce systemic risk, enable the safe scaling of AI agents, and protect user privacy in an automated world.
More recently, Hardt has been a leading voice in the Agentic AI space, bridging the gap between LLM capabilities and infrastructure security. Through his venture Hello, he connects identity design with the broader challenge of creating user-sovereign digital assistants. This work is becoming critical as the Model Context Protocol and other agentic frameworks require a robust, standardized identity layer to transform AI from a passive tool into an accountable digital teammate.
Resources & Events
📅 apidays Singapore (Marina Bay Sands, Singapore - April 14-15, 2026)
apidays Singapore brings together API builders, architects, and platform leaders in one of Asiaʼs biggest fintech and digital transformation hubs, with a strong focus on how APIs are evolving for the AI and agentic era. The program blends practical case studies and technical sessions across API management, security, governance, and automation. Details →
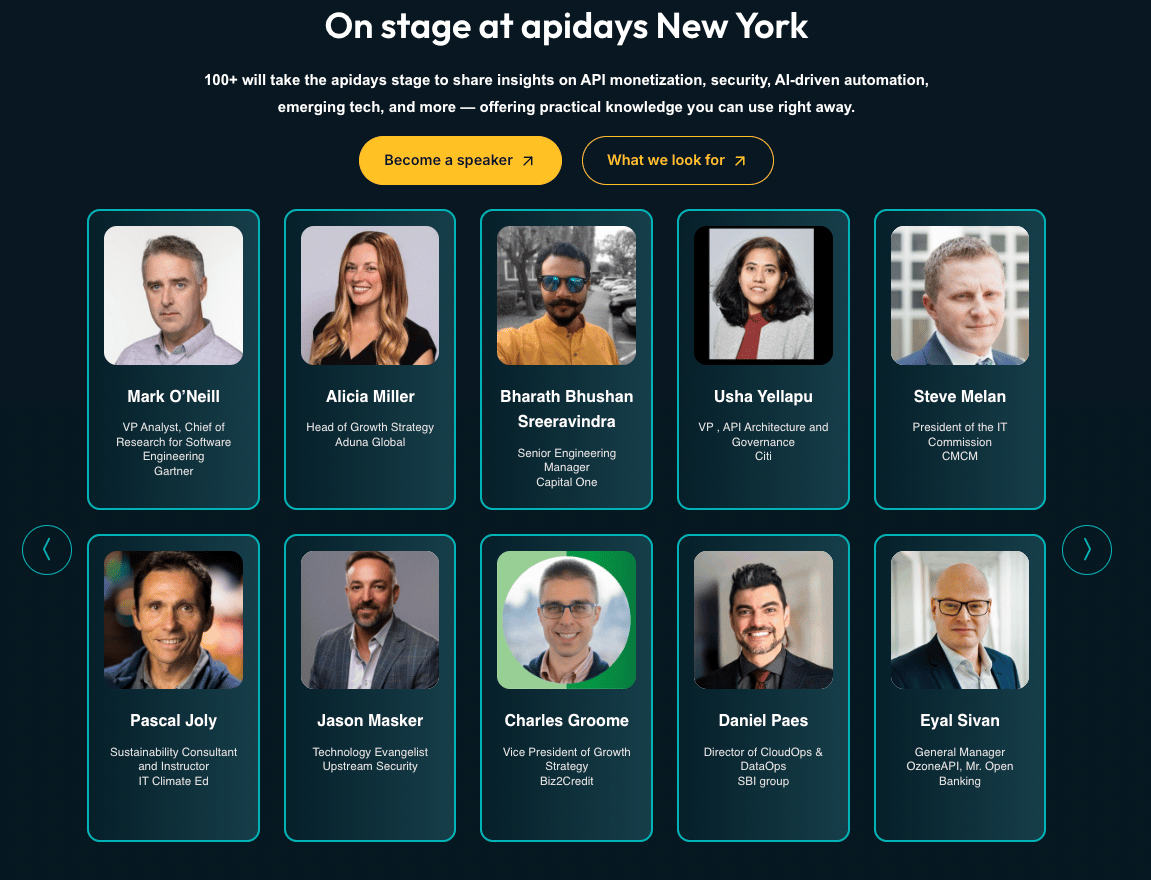
📅 apidays New York (Convene 360 Madison, New York - May 13-14, 2026)
apidays New York is positioned as a high-density gathering for teams operating APIs at scale, with sessions spanning monetization, security, AI-driven automation, and platform governance. Itʼs built for senior practitioners and decision-makers, bringing together 1,500+ participants from 1,000+ companies, making it a strong anchor event for anyone tracking where enterprise API strategy is heading next. Details →
You can find a list of all Apidays events here
Apply to speak at Apidays Singapore, NY, London, Paris, and more here
📅 JAX London 2026 (London, UK - October 5-9, 2026)
JAX London focuses on high-performance Java, microservices architecture, and modern API engineering. The program features deep dives into REST and gRPC performance, cloud-native integration patterns, and the evolution of JVM-based backend systems for scalable enterprise environments. Details →
📊 Report Spotlight: 2026 Agentic Trends Report (MuleSoft)
Agentic AI is fundamentally transforming enterprise automation from static, rules-based workflows into dynamic networks of autonomous agents. Industry forecasts indicate that agentic AI will account for $1.3 trillion in IT spending by 2029, with 40% of applications featuring task-specific agents as early as 2026. To maximize these benefits, organizations are shifting toward next-generation API management and composable architectures that prioritize agent actionability, secure data access, and real-time orchestration. Read →
Insight of the Week
Shifting from Raw Silicon to a Complete Software and Security Stack for Autonomous Agents
NVIDIA is pivoting from raw silicon to a complete software and security stack for autonomous agents. As enterprises shift toward long-running digital workers, trust and governance are now the primary bottlenecks. NVIDIA’s solution includes the Agent Toolkit, featuring the NemoClaw secure runtime for process-level isolation and the AI-Q open blueprint, designed to transform agentic AI into a strictly governed corporate asset.
For the Commute
Governance and Security of APIs and MCPs (apidays)
In this talk, API security expert Isabelle Mauny warns that the industry is repeating historical mistakes by building complex AI agents on top of unstable integration foundations. She argues that while the Model Context Protocol is a powerful tool for Agentic AI, it introduces significant risks, from token loops that cause massive cloud bills to security vulnerabilities where LLMs are tricked into deleting databases. She proposes a disciplined approach of securing the underlying API layer first, designing MCPs specifically for agent consumption, and applying strict identity and lifecycle governance to automated actors.
That’s it for this week.
Stay tuned for bold ideas, fresh perspectives, and the next wave of API innovation
-The Apidays Team